Difference between revisions of "Single Sign-On (SSO)"
IVSWikiBlue (talk | contribs) |
IVSWikiBlue (talk | contribs) |
||
| (3 intermediate revisions by the same user not shown) | |||
| Line 1: | Line 1: | ||
__NOTOC__ | __NOTOC__ | ||
{{Article | title = SSO Configuration | content = | {{Article | title = SSO Configuration | content = | ||
| − | {{Aside - | + | {{Aside - Helpful | content = VALT is compatible with <b>SAML 2.0</b>.}} |
{{Aside | content = To access SSO on your system, you may need to reach out to our support team. [https://ivs.help IVS Support]}} | {{Aside | content = To access SSO on your system, you may need to reach out to our support team. [https://ivs.help IVS Support]}} | ||
{{hr}} | {{hr}} | ||
| − | == | + | ==Scheduling an SSO Configuration== |
| − | Before configuring SSO in VALT, please make sure you've completed our [[SSO Check List]]. | + | {{Aside - Warning | hue = 50 | content = Before configuring SSO in VALT, please make sure you've completed our [[SSO Check List]].}} |
| − | You can also schedule a <b>SSO Discovery</b> at our [https://ivs.help booking site] under <b>Schedule a Support Session</b>. | + | You can also schedule a <b>SSO Discovery</b> at our [https://ivs.help booking site] under <b>Schedule a Support Session</b>. During that call, we will discuss the prerequisites for configuring your VALT server to utilize SSO Authentication. |
{{hr}} | {{hr}} | ||
| − | + | <h2>SSO Authentication</h2> | |
| − | + | SSO accounts are automatically created when a user logs in for the first time. The user can be placed in the proper group automatically upon login by mapping SSO attributes to a user group within VALT. | |
| − | + | ||
| − | < | + | *VALT's SSO uses <b>Just-In-Time (JIT) Provisioning</b>. |
| − | < | + | **<em>Users are reevaluated and assigned to groups each time they log in, based on a [[Single_Sign-On_(SSO)#User_Mapping | group membership]] attribute being passed.</em> |
| − | < | + | *If a user does <u>NOT</u> have a user mapping associated with their account, the user gets moved to "<b>Users without Group</b>" and has restricted access. |
| − | + | *If a user's user mapping changes, they will be moved to the correct group upon their next SSO sign-in. | |
| − | < | + | **<em>Correct mapping is based on the SSO mapping created in VALT and the attribute/pair value being passed from the IdP.</em> |
| − | + | ||
| − | < | + | {{hr - 2}} |
| − | + | ||
| − | + | {{img - resize | file = SSO Flow Chart.png}} | |
{{hr}} | {{hr}} | ||
| − | < | + | ==Required Information from IdP== |
| − | + | <dt>IdP Metadata File</dt> | |
| + | <dd class="singleLineHeight">To integrate your IdP with VALT, the metadata files from both will need to be exchanged. The VALT metadata file will be generated after the IdP metadata file is uploaded to VALT.</dd> | ||
| + | <dt>User Mapping</dt> | ||
| + | <dd class="singleLineHeight">VALT's SSO uses a 1:1 mapping to add users to the correct groups. To achieve this, we require the following attributes: | ||
| − | + | <b>Unique User Identifier</b> - This attribute will be used as the username | |
| − | < | + | <b>Groups</b> - This attribute will be used to define which group the user is assigned to within VALT. In addition to the name of the Group attribute, VALT will need the value associated with each group that will be logging into VALT |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | {{hr}} | + | <b>Display Name</b> - If the Unique User identifier does not correspond with the person's name, this attribute will set an easy-to-identify display name for the user</dd> |
| + | {{hr - 2}} | ||
<h3>Optional Items</h3> | <h3>Optional Items</h3> | ||
| Line 53: | Line 46: | ||
<dl> | <dl> | ||
| − | <dt> | + | <dt>PIN</dt> |
| − | |||
| − | |||
| − | |||
<dd class="singleLineHeight">This specifies the code used for authentication into [[BEAM]].</dd> | <dd class="singleLineHeight">This specifies the code used for authentication into [[BEAM]].</dd> | ||
<dd class="singleLineHeight"><em>Without one set, no pin is needed to enter BEAM</em>.</dd> | <dd class="singleLineHeight"><em>Without one set, no pin is needed to enter BEAM</em>.</dd> | ||
Revision as of 11:57, 22 November 2024
SSO Configuration
🕮VALT is compatible with SAML 2.0.
✎To access SSO on your system, you may need to reach out to our support team. IVS Support
Scheduling an SSO Configuration
⚠Before configuring SSO in VALT, please make sure you've completed our SSO Check List.
You can also schedule a SSO Discovery at our booking site under Schedule a Support Session. During that call, we will discuss the prerequisites for configuring your VALT server to utilize SSO Authentication.
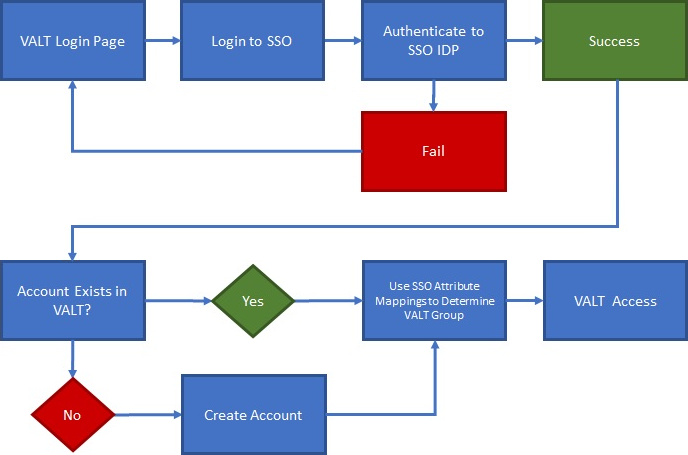
SSO Authentication
SSO accounts are automatically created when a user logs in for the first time. The user can be placed in the proper group automatically upon login by mapping SSO attributes to a user group within VALT.
- VALT's SSO uses Just-In-Time (JIT) Provisioning.
- Users are reevaluated and assigned to groups each time they log in, based on a group membership attribute being passed.
- If a user does NOT have a user mapping associated with their account, the user gets moved to "Users without Group" and has restricted access.
- If a user's user mapping changes, they will be moved to the correct group upon their next SSO sign-in.
- Correct mapping is based on the SSO mapping created in VALT and the attribute/pair value being passed from the IdP.
Required Information from IdP
Unique User Identifier - This attribute will be used as the username
Groups - This attribute will be used to define which group the user is assigned to within VALT. In addition to the name of the Group attribute, VALT will need the value associated with each group that will be logging into VALT
Display Name - If the Unique User identifier does not correspond with the person's name, this attribute will set an easy-to-identify display name for the user
Optional Items
VALT is also able to map custom attributes to some of the following fields for a user. Below are the user account fields that can be assigned through SSO.
- PIN
- This specifies the code used for authentication into BEAM.
- Without one set, no pin is needed to enter BEAM.
- Card Number
- This specifies the card number associated with a user.
- Only applies to customers with VALT Card Reader.
- The users email can also be pulled into the system.
- If the VALT application is not connected to mail server, this field is not used for anything.
Additional Settings
Shibboleth needs the following settings configured to function with VALT.
- signAssertions:
- true
- signResponses:
- true
- encryptNameIDs:
- true
- encryptAssertions:
- false
⤺ Back to VALT SSO Main Page