Difference between revisions of "SSO Check List"
IVSWikiBlue (talk | contribs) |
IVSWikiBlue (talk | contribs) |
||
| Line 9: | Line 9: | ||
=={{Checkbox - checked | item = SSO Checklist}}== | =={{Checkbox - checked | item = SSO Checklist}}== | ||
| − | *{{Checkbox - empty | item = | + | *{{Checkbox - empty | item = Server racked and patched}} |
| − | *{{Checkbox - empty | item = | + | *{{Checkbox - empty | item = SSL certificate and NTP server installed}} |
**{{Checkbox - empty | item = Understanding of VALT group mappings}} | **{{Checkbox - empty | item = Understanding of VALT group mappings}} | ||
**{{Checkbox - empty | item = Understanding of user creation and management}} | **{{Checkbox - empty | item = Understanding of user creation and management}} | ||
| − | |||
| − | |||
}} | }} | ||
Revision as of 16:49, 6 October 2023
Contents
Where to Begin?
Before SSO is configured on your VALT server, there are a few things that need to be done, setup, and understood. This article aims to help you identify where you are in the process and what steps might need to be done before you configure SSO on your server!
The following list of items should be done, in order. Identifying where you are in this process is your first step.
☑ SSO Checklist
☐ Server racked and patched
☐ SSL certificate and NTP server installed
☐ Understanding of VALT group mappings
☐ Understanding of user creation and management
- Browse to the the Fully qualified domain name and sign in with a local account
- Click on admin
- Click on Users & Groups
- Along the top click on SSO and add SAML config
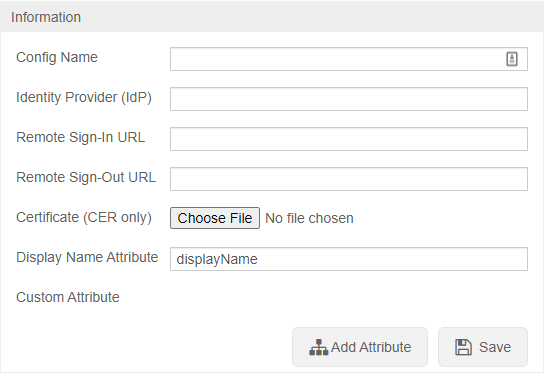
To configure SSO VALT needs the following information:
- Certificate in .cer format
- Identity Provider (IDP)
- Remote Sign-In URL
- Remote Sign-Out URL
- Display Name Attribute
- Any other custom attributes needed
After SSO is configured browse to https://<Server Address>/saml/metadata.xml to grab the VALT metadata to add to your system
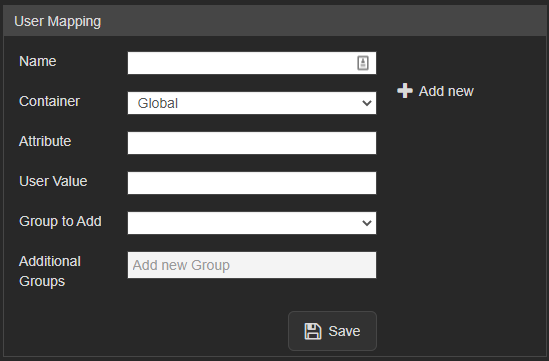
User Mapping
Required
Users are mapped to VALT groups using attributes and values being passed from the IdP.
- Name
- The value to define the mapping. Used only in this section of VALT.
- Attribute
- The item that gets passed back to VALT.
- User Value
- The value of the item that gets passed back to VALT.
- Group to Add
- The group created on the VALT side that defines the user's rights in the application.
Other Notes
Moving from LDAP to SSO
- If moving from LDAP to SSO you have to add a custom attribute to map to the username so the usernames will match correctly
- To migrate current users to SSO the SQL command needs to be run on the database with the correct group ID
UPDATE users set ldap_sync_id = NULL, saml_config_id = 1, userType = 'local' where deleted_at is null and group_id =
Custom Attributes
- Custom Attributes can be usernames if you want to map to something specific or other information that you want to pull into VALT
Additional Settings
- Shibboleth IDP's need the following settings specified:
- signAssertions:
- true
- signResponses:
- true
- encryptNameIDs:
- true
- encryptAssertions:
- false