Single Sign-On (SSO)
Revision as of 08:52, 19 September 2023 by IVSWikiBlue (talk | contribs)
✎
VALT is compatible with SAML 2.0
To Begin
- Browse to the the Fully qualified domain name and sign in with a local account
- Click on admin
- Click on Users & Groups
- Along the top click on SSO and add SAML config
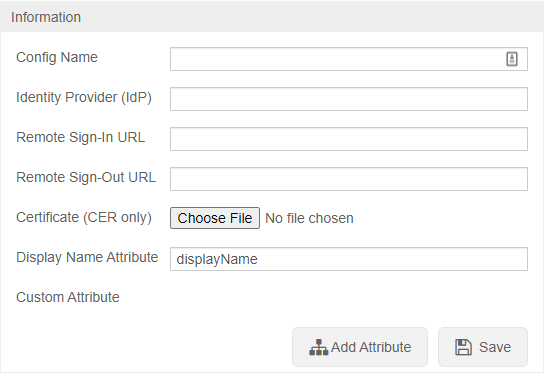
To configure SSO VALT needs the following information:
- Certificate in .cer format
- Identity Provider (IDP)
- Remote Sign-In URL
- Remote Sign-Out URL
- Display Name Attribute
- Any other custom attributes needed
https://<Server Address>/saml/metadata.xml to grab the VALT metadata to add to your systemUser Mapping
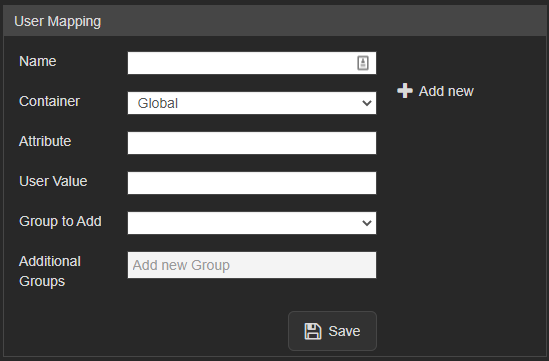
User mapping is used to map groups in the customer's system to groups within VALT
✎
NOTE: SSO in VALT is a one to one mapping for groups
Required
Users are mapped to VALT groups using attributes and values being passed from the IdP.
- Name
- The value to define the mapping. Used only in this section of VALT.
- Attribute
- The item that gets passed back to VALT.
- User Value
- The value of the item that gets passed back to VALT.
- Group to Add
- The group created on the VALT side that defines the user's rights in the application.
Other Notes
Moving from LDAP to SSO
- If moving from LDAP to SSO you have to add a custom attribute to map to the username so the usernames will match correctly
- To migrate current users to SSO the SQL command needs to be run on the database with the correct group ID
UPDATE users set ldap_sync_id = NULL, saml_config_id = 1, userType = 'local' where deleted_at is null and group_id =
Custom Attributes
- Custom Attributes can be usernames if you want to map to something specific or other information that you want to pull into VALT
Additional Settings
- Shibboleth IDP's need the following settings specified:
- signAssertions:
- true
- signResponses:
- true
- encryptNameIDs:
- true
- encryptAssertions:
- false