Single Sign-On (SSO)
Revision as of 17:19, 22 August 2023 by IVSWikiBlue (talk | contribs)
✎VALT is compatible with SAML 2.0
✎VALT is compatible with SAML 2.0
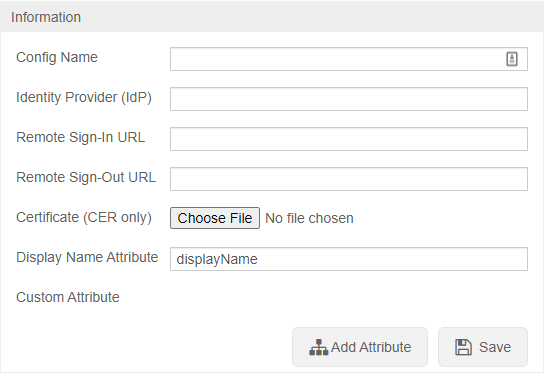
After SSO is configured browse to https://<Server Address>/saml/metadata.xml to grab the VALT metadata to add to your system
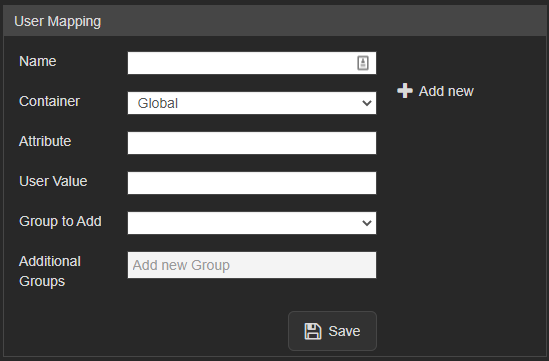
✎NOTE: SSO in VALT is a one to one mapping for groups
Users are mapped to VALT groups using attributes and values being passed from the IdP.
UPDATE users set ldap_sync_id = NULL, saml_config_id = 1, userType = 'local' where deleted_at is null and group_id =
signAssertions: true signResponses: true encryptNameIDs: true