Difference between revisions of "CVE-2021-44228"
IVSWikiBlue (talk | contribs) |
IVSWikiBlue (talk | contribs) |
||
| Line 1: | Line 1: | ||
=Vulnerability= | =Vulnerability= | ||
https://nvd.nist.gov/vuln/detail/CVE-2021-44228 | https://nvd.nist.gov/vuln/detail/CVE-2021-44228 | ||
| + | https://nvd.nist.gov/vuln/detail/CVE-2021-45046 | ||
'''Based on the information available regarding the vulnerability and how the affected packages are utilized in VALT, we do not believe at this time that the vulnerability can be exploited on any VALT servers. Additionally most customers are operating VALT isolated within their own network, so the risk is low that a malicious party could connect to a VALT server to attempt to exploit the vulnerability. However in effort to ensure your security, we have provided the information below on how to address this vulnerability.''' | '''Based on the information available regarding the vulnerability and how the affected packages are utilized in VALT, we do not believe at this time that the vulnerability can be exploited on any VALT servers. Additionally most customers are operating VALT isolated within their own network, so the risk is low that a malicious party could connect to a VALT server to attempt to exploit the vulnerability. However in effort to ensure your security, we have provided the information below on how to address this vulnerability.''' | ||
| Line 14: | Line 15: | ||
Intelligent Video Solutions recommends that you updated your VALT server to the latest release. The latest release includes a fix to this vulnerability. You can book an update with an IVS support engineer at http://ipivs.com/book. | Intelligent Video Solutions recommends that you updated your VALT server to the latest release. The latest release includes a fix to this vulnerability. You can book an update with an IVS support engineer at http://ipivs.com/book. | ||
| − | If you are unable to update your system, you can follow the steps below to address this specific vulnerability. | + | If you are unable to update your system, you can follow the steps below to address this specific vulnerability. This remediation has been updated to address both CVE-2021-44228 and CVE-2021-45046. |
'''WARNING: The steps below outline using an automated script to update the VALT appliance. It is designed to be used on standard Valt appliances.''' | '''WARNING: The steps below outline using an automated script to update the VALT appliance. It is designed to be used on standard Valt appliances.''' | ||
Revision as of 10:31, 16 December 2021
Vulnerability
https://nvd.nist.gov/vuln/detail/CVE-2021-44228 https://nvd.nist.gov/vuln/detail/CVE-2021-45046
Based on the information available regarding the vulnerability and how the affected packages are utilized in VALT, we do not believe at this time that the vulnerability can be exploited on any VALT servers. Additionally most customers are operating VALT isolated within their own network, so the risk is low that a malicious party could connect to a VALT server to attempt to exploit the vulnerability. However in effort to ensure your security, we have provided the information below on how to address this vulnerability.
Affected Versions
This vulnerability is only present VALT servers running version 5.5 and higher. Older VALT servers are unaffected by the vulnerability.
You can check your VALT version on the General page under the Admin section.
https://ipivs.info/wiki/index.php/VALT_Administrator_Guide_5.5#General
Remediation
Intelligent Video Solutions recommends that you updated your VALT server to the latest release. The latest release includes a fix to this vulnerability. You can book an update with an IVS support engineer at http://ipivs.com/book.
If you are unable to update your system, you can follow the steps below to address this specific vulnerability. This remediation has been updated to address both CVE-2021-44228 and CVE-2021-45046.
WARNING: The steps below outline using an automated script to update the VALT appliance. It is designed to be used on standard Valt appliances.
WARNING: This applies to VALT 5.5 - 5.5.8. DO NOT PERFORM THESE STEPS ON ANY OTHER VERSION!!
- Log into the Valt appliance via SSH or the terminal
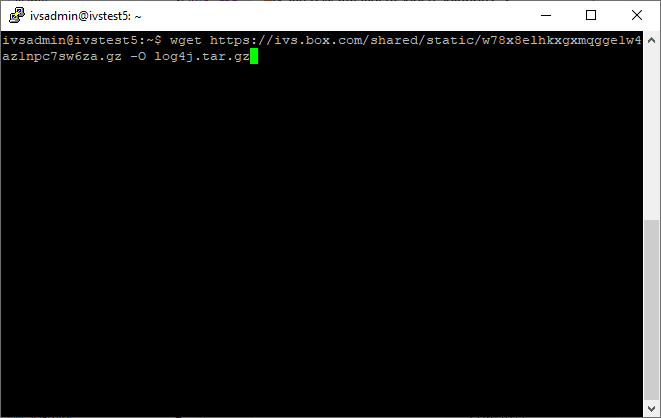
- Type in the following, followed by pressing Enter:
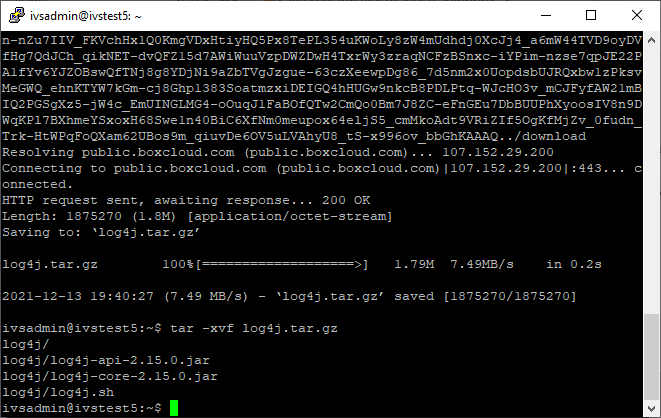
wget https://ivs.box.com/shared/static/w78x8elhkxgxmqgge1w4az1npc7sw6za.gz -O log4j.tar.gz - Type in the following, followed by pressing Enter:
tar -xvf log4j.tar.gz - Type in the following, followed by pressing Enter:
cd log4j - Type in the following, followed by pressing Enter:
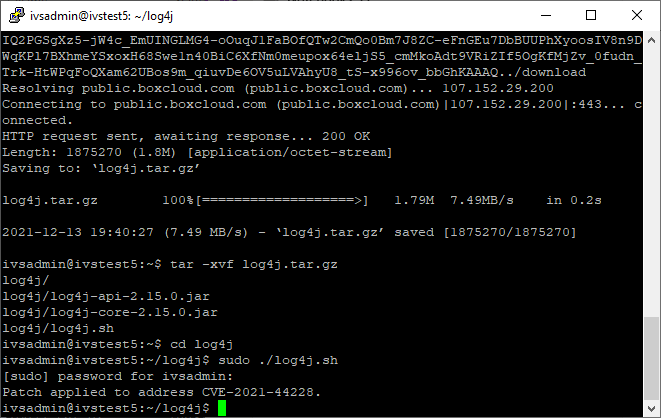
sudo ./log4j.sh - Enter the password if prompted.
- The vulnerability has now been patched.